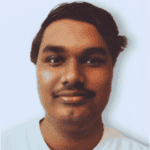
AI website builders can take a WordPress site from prompt to production in minutes. But that scale creates new security challenges that most agency workflows aren’t built to handle.
10Web’s agentic AI Builder enforces necessary guardrails at the process level, not individually per site. Here’s how we recommend adapting your agency’s development and production workflow for AI generated website security.
How does AI impact WordPress security?
AI generators aren’t yet trained to have the security judgment of a senior developer. They produce what they’re configured to produce. For an open-ended platform like WordPress, the community-powered plugin and theme ecosystem carries inherent risk.
AI doesn’t add new risk factors so much as it changes how you address existing ones. When a platform ships dozens of sites with preset configurations, a single vulnerability becomes a portfolio-wide issue. Whereas a traditional agency building sites one at a time can catch security issues during testing, an agency generating ten sites a week can’t rely on that pace.
Security researchers call this replication risk. A single configuration issue or unpatched component gets copied over across multiple deployments, spreading to your entire fleet of websites before anyone flags it. It’s not a hypothetical risk, it’s the default outcome when security isn’t built into the AI generation system.
With AI, you’re no longer securing a website, you’re securing the system that produces websites. That’s why a post-launch checklist isn’t enough to solve this. The answer is a platform that builds protection into the generation and hosting pipeline from the start.

Turn AI speed into safe production
Launch WordPress sites with security, monitoring, and governance built in from day one.
A practical threat model for AI-generated WordPress sites
Our threat model for AI-built WordPress sites isn’t a list of vulnerabilities to patch. It’s a map of where operational and process failures concentrate when you’re building and managing sites at scale. Five categories account for most things that can go wrong in AI-generated WordPress deployments.
Authentication, permissions, and access control
When controls like 2FA requirements, least-privilege access scoping, or authentication hardening aren’t enforced at the platform level, every site ships with the same weak defaults. This is made worse by overprivileged guest accounts that never get decommissioned after use. Creating a proper access management system that plugs dormant entry points is the only way to address this systematically.
Code vulnerabilities in themes and plugins
Community-built plugins and themes are the highest-risk surface in any WordPress deployment. Keeping components updated, removing abandoned plugins, and vetting what gets installed is manageable on a single site, but unreliable and error-prone across dozens. If your AI platform doesn’t have a curated allow-list and automated vulnerability tracking, sites inherit the full risk inventory of the ecosystem.
Infrastructure-level issues
WordPress servers get configured once at deployment and rarely revisited. That works until you’re managing a portfolio of sites with drifting PHP versions and inconsistent WAF coverage. Without standardized hosting policies enforced across the fleet, server-level protections get skipped and compromise every website sharing the same hosting container.
Data exposure risk
When deadlines are rushed, API keys end up in theme files, backup archives land in accessible directories, order data sits unencrypted at rest. For sites handling payments or customer data, that creates regulatory exposure under GDPR, CCPA, or PCI-DSS. At scale, these isolated oversights evolve into full-blown operational gaps.
Ongoing maintenance woes
WordPress security isn’t just a launch condition, it’s an operational requirement that gets glossed over in the post-production stage. Attackers often begin exploiting newly disclosed vulnerabilities within 24 hours of publication. Staying ahead of that cadence across a large fleet requires automated patching and centralized visibility that many agencies don’t have.
| Threat category | Attack surface | Attack vectors | Area of impact | Mitigation controls |
| Authentication & access | No credential policies, no 2FA, excess access, stale accounts | Brute force, credential stuffing, password spraying | Admin takeover, malware, data theft, lockout | Enforce 2FA, strong credential rules, access audits, least privilege |
| Theme & plugin vulnerabilities | Unvetted plugins, abandoned components, no allow-list | RCE, privilege escalation, XSS | Fleet-wide compromise through shared components | Use vetted allow-lists, patch fast, remove inactive plugins |
| Infrastructure issues | Inconsistent PHP, no WAF, shared hosting without isolation | SQL injection, DDoS, SSRF | Server-wide failure across co-hosted sites | Standardize hosting, verify WAF/PHP, isolate client containers |
| Data exposure | No storage standards, exposed backups, unencrypted data | Data exfiltration, MitM, IDOR | Customer data, payments, credentials, compliance risk | Secure storage defaults, off-site backups, SSL auto-renewal |
| Maintenance gaps | No update automation, ad hoc patching, no monitoring | Known CVEs, malware injection, silent compromise | Security debt and delayed patching across sites | Automate updates, centralize monitoring, add security agents |
How to secure a WordPress site at the system level
The five threat categories above share a common characteristic: they’re most effectively addressed at the platform level, not the site level. Per-site security reviews don’t scale with AI generation. What scales is a platform that enforces security defaults consistently across every site it deploys.
10Web is built around this principle. Its managed infrastructure, agent-based lifecycle management, and governance tooling address the structural risks that AI generation introduces. None of it is left for the agency to handle manually after launch.
Infrastructure defaults that remove per-site configuration risk
Every site 10Web hosts runs inside an isolated Linux container. A misconfiguration or compromise on one client’s site can’t propagate to others on the same infrastructure. Replication risk is contained by design.
At the network level, all hosted sites run behind a Cloudflare Enterprise WAF with DDoS and bot protection. It enforces automatic login attempt limiting by default and blocks suspicious bots before they reach your site. Free Let’s Encrypt SSL certificates are provisioned on all plans and renew automatically. These infrastructure-level protections apply to every site generated through 10Web by default.
Fleet-level governance for agencies and MSPs
Managing security across a large portfolio requires centralized visibility. 10Web’s multi-site dashboard supports hundreds of sites from a single interface, with centralized plugin and theme update management, detailed activity logs, and PHP version control across the fleet. You can push updates across multiple client sites at once. You can audit what changed without logging into each one individually. That matters when a critical vulnerability drops and you need to act fast.
A curated plugin ecosystem and active vulnerability management
10Web addresses plugin risk at the source. The platform maintains an up-to-date list of known vulnerable plugins and themes. Agent-based generation installs components from a vetted allow-list rather than pulling from the broader WordPress ecosystem without checking. That addresses plugin and theme risk before generation, not after.
For ongoing management, 10Web’s security service monitors hosted sites continuously for malware, unauthorized changes, and suspicious activity. When a threat is detected, the platform initiates malware removal and notifies the site owner. That response loop operates at the infrastructure level, not through site-level security plugins.
Backup, recovery, and a staging layer for safe updates
10Web’s managed hosting includes automatic daily backups stored in the cloud, with restore capability directly from the dashboard. Higher-tier plans add real-time and incremental options. Every plan also includes a staging environment. High-severity plugin and core updates can be tested before they touch a live site, closing the gap between vulnerability disclosure and safe deployment.
Ongoing security maintenance through post-launch agents
10Web’s agentic AI continues working after launch, handling performance monitoring, security patches, and content updates as an ongoing background process. For agencies managing large client portfolios, that replaces a recurring manual task with continuous system-level coverage. No separate security operations function is required.

Turn AI speed into safe production
Launch WordPress sites with security, monitoring, and governance built in from day one.
Security that’s built into your workflow, not added on top
Speed creates conditions where security gaps can replicate across your entire client base before anyone catches them. Addressing that one site at a time defeats the point of AI generation.
10Web is built with that reality taken into account. Security defaults are enforced at the infrastructure layer. Components are pulled from a vetted ecosystem. Agents monitor and patch your CMS continuously. You get automated security hardening at scale with detailed activity logging.
On top of all that, fleet-level governance gives you top-down visibility across every site you manage.
FAQ
Are AI-generated WordPress websites secure by default?
AI builders accelerate production, but without platform-level safeguards, they can replicate the same vulnerabilities across multiple sites. Security must be enforced at the system level, not added after launch.
What is “replication risk” in AI website generation?
Replication risk is when a single misconfiguration or vulnerability gets copied across every generated site. Instead of one insecure website, you end up with a fleet-wide exposure that scales with your production.
What are the biggest security risks for AI-generated WordPress sites?
The most common risks include weak authentication controls, vulnerable plugins and themes, inconsistent infrastructure, exposed data, and lack of ongoing maintenance. These risks compound when managing multiple sites at scale.
Why doesn’t a post-launch security checklist work for AI-built sites?
Because AI changes the scale of deployment. Manual reviews don’t keep up when sites are generated rapidly, so security must be embedded into the generation and hosting pipeline instead of handled per site.
How can agencies secure multiple WordPress sites built with AI?
By using platforms that enforce standardized security policies and centralized monitoring across all sites simultaneously rather than managing each one individually.